What is 2FA and why you should enable it now
We are storing more important personal information online than we ever have before. Keeping it private and secure is, therefore, becoming increasingly important. Two-Factor Authentication or 2FA is here to lend a hand.
Written by human for humans
[February 2024 update: This post is archived. Check out our latest article on two-factor authentication and learn how to enable it on Koofr.]
To protect our personal information online and keep them private, we need to make sure we're the only ones able to access them. That is done through a process called authentication. You need to correctly "introduce" yourself to the service and prove that you're really you before you can enter.
There are three widely accepted methods of authenticating yourself:
- Knowledge – something you know. Passwords, PIN numbers and patterns to unlock your smartphone all fall into this category. It's a simple, yet not very secure method. Much has been written about the problems with "strong" passwords, people using the same password for different services and similar issues, so at this point, we just want to emphasize that passwords can be problematic.
- Possession – something you own. Smart cards, tokens, similar devices, and in simplified terms also your phone. These types of authentication are commonly a part of the multifactor authentication process.
- Inherence – something you are. Biometric types of authentication fall into this field –fingerprints, facial scans, retinal scans, voice patterns etc. The jury is still out on the pros and cons of this type of authentication, mostly because it opens a whole new field of privacy issues, poses high costs and is still not 100% hack-proof.
What is Two-Factor Authentication?
Two-factor authentication (2FA) is a very efficient way to secure your accounts and digital assets. It's like an extra layer of protection. It combines the password (something you know) with a second factor, like a one-time passcode or push notification sent to your mobile phone (something you own).
Note: You will also see names like Two-Step Verification, Multifactor authentication and similar. While there are certain technical differences between them, at this point we won't get into details.
Why does it matter?

As we have established, passwords are weak and even the most complex ones don't necessarily protect you from hacking attacks. Two-factor authentication requires two different keys to log you into your account, significantly decreasing the risk of account takeovers. Using a Two-Factor Authentication process can help avoid identity theft, as well as phishing via email because the criminal would need more than your name and password.
Online security experts strongly suggest enabling 2FA on all your online accounts; including email accounts, social networks, online banking, e-commerce sites, cloud computing etc.
Check out our video on 2FA.
2-Step verification in Koofr
Koofr offers 2-Step Verification to protect your account with an additional layer of security. To start using it, you just need to follow a few simple steps.
First, head to your Koofr account, click on Preferences in the Account Settings Menu and choose 2-Step Verification on the left.
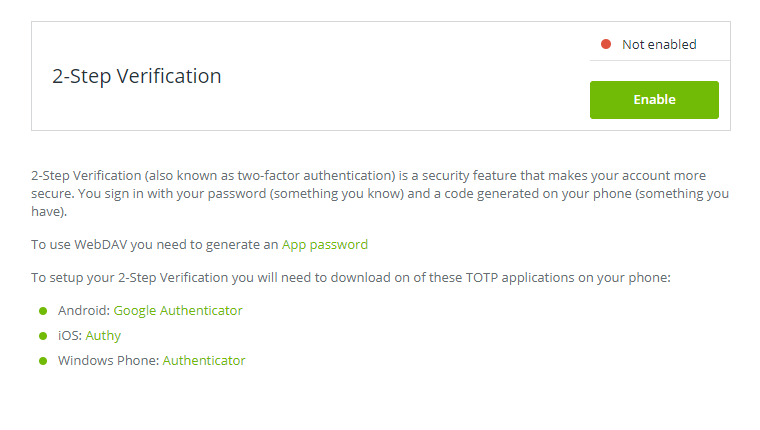
Next, download a suitable TOTP ((Time-based One-time Password Algorithm) mobile application for your phone. This app will turn your phone into a device capable of 2-Step Verification.
- Android: Google Authenticator
- iOS: Authy
- Windows Phone: Authenticator
When you have your mobile app installed, open it. After clicking on the Enable button a dialogue with a barcode will appear. Scan the code with your mobile app and follow the instructions in the app – you will need to enter the code from the app into the field below the barcode.
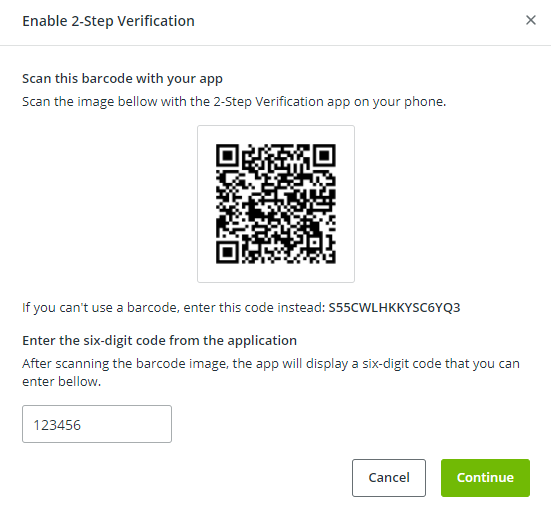
Click Continue, then save your Recovery codes somewhere safe and click Enable.
Note: Your Recovery codes are the only way for you to recover access to your account if you lose access to your device and cannot access 2-Step Verification codes generated on your TOTP mobile application. Our support team cannot restore access to accounts with 2-Step Verification enabled for security reasons, which means you will permanently lose access to your Koofr account without your Recovery codes. They are super important, so make sure you store them in a secure place.
You’re all set and your Koofr files are now even safer.
Want to talk to us? Join us on the Koofr subreddit!


